We have been subjecting our infrastructure and applications to annually-recurring penetration tests for years. However, last week, a different penetration “test” took place… and as it turns out: inadvertently!
Someone broke into our offices by forcing a window open, went through our office space, even broke into our server-room, and left with … nothing?!
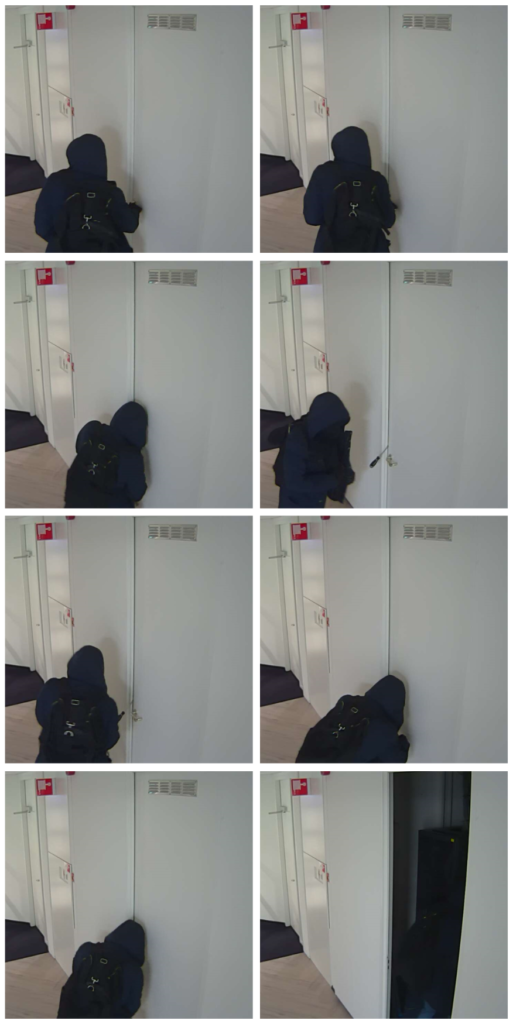
Of course, we were shocked at first! We saw on photos taken by our security-cameras the perpetrator using a screwdriver and brute-force to open locked doors and we saw the perpetrator moving swiftly from room to room…
The next morning we took inventory of the damage and also of all computer equipment that was in the office. We have been maintaining a detailed and up-to-date Inventory of Assets and could quickly conclude that there was nothing missing! This was in accordance with our expectation after the initial study of the security-camera footage: the perpetrator spent a meagre 7 seconds in our server-room, leaving the room while still holding the screwdriver in one hand, as when entering it. Moreover, the entire “visit” in our office space took no more than 3 minutes or so.
Nonetheless, we checked carefully whether tampering with any systems had taken place (e.g. by leaving a USB-Stick inserted, adding/removing cables, re-wiring components, etc.) but again, this was not found to be the case.
And, thus, we were (and still are) somewhat baffled as to the purpose of the break-in.
Our hunch is that it was totally unexpected that all the office lighting would turn on triggered by movement sensors. Additionally, because the office has mostly glass walls, there is hardly any place one can stay out-of-sight from bypassers (mind you, it was dark outside and brightly illuminated inside and still quite some people were leaving their offices). And last, but not least, the presence of our security-cameras might have also indicated that a silent alarm had been raised and time was limited…
So, all’s well that ends well!
And then we realised that we had a unique opportunity at hand and decided to treat this incident as a (physical) penetration test! We looked at what went well for us and what could have gone worse. We realised that our Clear-Desk, Clear-Screen, and Password Protection policies, as well as our Asset Management are working efficient! And as an improvement, we will soon be adding a security-camera for an area that was not entirely covered.
Of course, we would have rather had this test be played out as a simulated test than be confronted with this real-life situation; but we will grab any opportunity to learn from this incident!